DE | EN

Most sensor-based models are not validated
where risk becomes critical
We analyze sensor data where standard methods break down: rare events, subtle deviations, and critical system behavior.
Services
In many industrial applications, models perform reliably under normal conditions – until rare events occur or system behavior changes subtly.
Detection and analysis of critical anomalies
Detection of deviations that are missed by simple thresholds and
standard modeling approaches.
Typical issue:
Individual deviations trigger isolated alarms without context. This leads to critical developments being either missed or misinterpreted as separate, unrelated events.
Statistical quantification of rare events
Assessment of risks in regions where data is scarce and
standard statistical methods break down.
Typical issue:
It is often unclear when a deviation becomes relevant. Short-lived events are overemphasized, while sustained critical conditions are underestimated due to the lack of a temporal perspective.
Validation of model behavior
Assessing whether models remain stable under real-world conditions, especially beyond their typical operating range.
Typical issue:
Models react to individual signals without considering their temporal structure. As a result, false alarms occur, or systems appear stable while critical developments go undetected.
Applications & Approach
1. Too many false alarms in stable systemsProblem:
A sensor system triggers frequent alarms despite stable operation. Thresholds react to individual outliers without considering their temporal context.Approach:
Analyzing the temporal structure of deviations and aggregating individual events into coherent patterns to reduce false alarms while maintaining sensitivity to critical developments.
2. Rare events are underestimatedProblem:
Critical events occur infrequently and are barely represented in historical data. Standard methods do not provide reliable risk assessments in the tails.Approach:
Analyzing extreme observations and modeling rare events to realistically assess risks in the tails, based on statistical methods for extreme value analysis.
3. Models work well in test environment but fail in real operationProblem:
A model shows stable results on validation data but behaves inconsistently in real-world operation. Model validation does not cover critical tail regions or changing system conditions.Ansatz:
Examining model behavior outside the typical operating range to reveal stability limits.
SigmaLens
Framework for anomaly analysis and model validation
SigmaLens is an analytical framework for the structured analysis of complex sensor data, with a focus on anomalies, rare events, and model behavior in tail regions.It combines signal modeling, residual analysis, and probabilistic assessment to identify critical developments under real-world conditions.
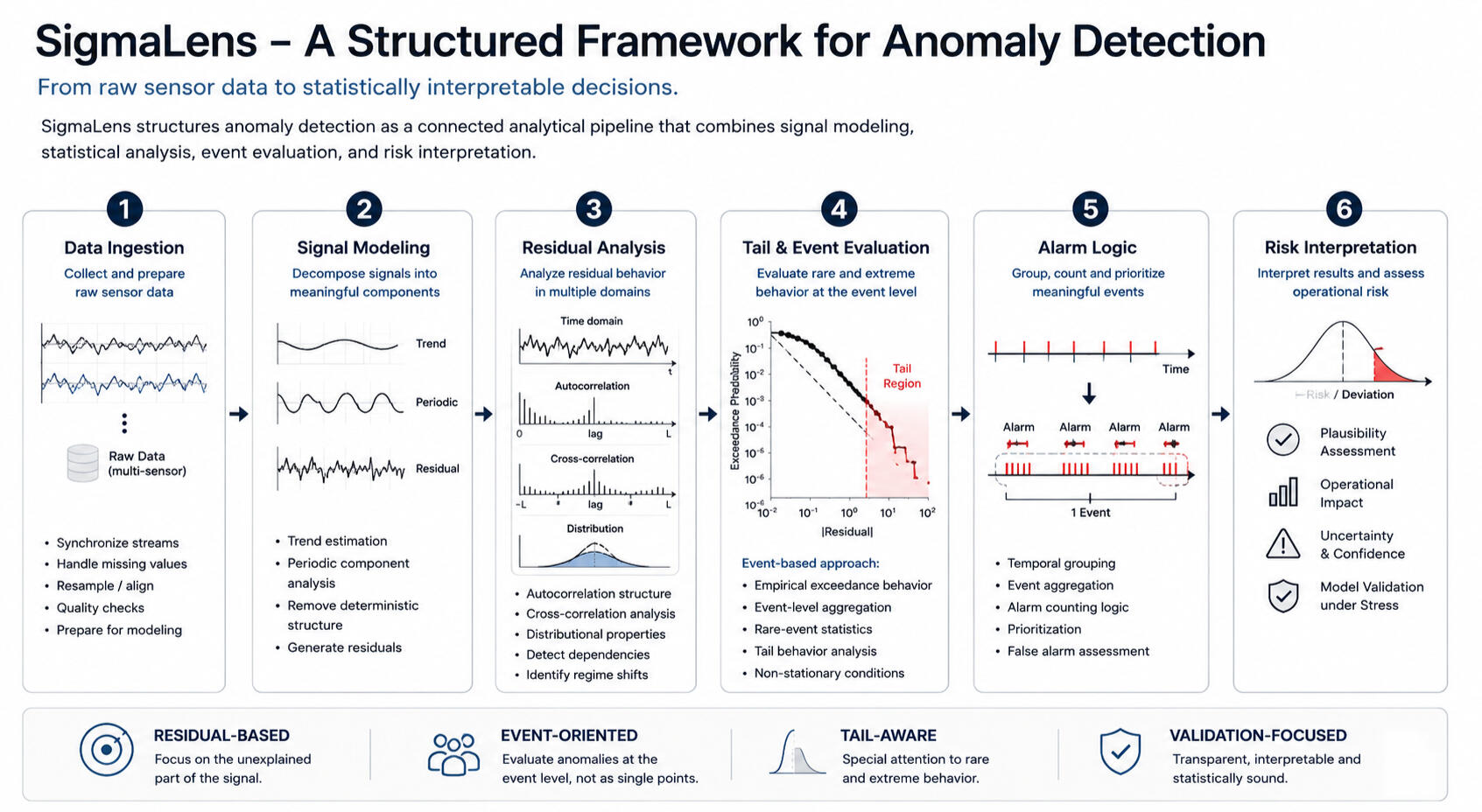
A detailed description of the analytical pipeline is available in the SigmaLens white paper.
About
Dr.-Ing. Majid Naeimi works on the statistical analysis of sensor data, with a focus on rare events, system behavior, and model stability. His work addresses areas where standard methods no longer provide reliable results, particularly in the tails and under uncertainty. He combines academic research with experience in industrial applications, particularly in the context of complex sensor-based systems.
Contact
Whether and where such issues occur in your systems can usually be assessed quickly. A short conversation is often sufficient to identify initial indications of
critical areas – without obligation.Email:
[email protected]
Impressum
DataSigma Analytics
Dr.-Ing. Majid Naeimi
Gartenstr. 7
74906, Bad Rappenau
E-Mail: [email protected]
Hinweis zur Tätigkeit: Statistische Beratung und Analyse im Bereich industrieller Sensordaten.
Datenschutzerklärung1. Verantwortlicher: Dr.-Ing. Majid Naeimi - DataSigma Analytics - Gartenstr. 7, 74906 Bad Rappenau, E-Mail: [email protected]
2. Hosting: Zur Bereitstellung dieser Website werden technisch notwendige Daten (z. B. IP-Adresse) verarbeitet.
3. Kontaktaufnahme per E-Mail: Wenn Sie per E-Mail Kontakt aufnehmen, werden Ihre Angaben zur Bearbeitung der Anfrage verwendet.
4. Externe Links: Diese Website enthält Links zu externen Anbietern (z. B. LinkedIn). Für deren Inhalte sind ausschließlich die jeweiligen Anbieter verantwortlich.
5. Rechtsgrundlage: Die Verarbeitung erfolgt auf Grundlage von Art. 6 Abs. 1 lit. f DSGVO sowie Art. 6 Abs. 1 lit. b DSGVO.